Recommended
Learn
Support
Crypto futures trading made easy
Enjoy the lowest fees on the market & up to 225x leverage
Popular futures
Start trading with low leverage
Sign upWhy choose BTCC
12 years of security
Protecting users' assets through many market cycles with 0 security incidents since 2011.
Industry-leading liquidity
Support orders from as small as 0.01 BTC to as big as 50 BTC. No slippage. Instant order execution.
Negative balance protection
BTCC absorbs the losses when your account goes below 0, so you will never lose more than you deposited.
Trading journey tailored to your levels and goals
I'm a beginner
I’m new to trading and need some help to guide me through all the steps.
I'm experienced
I am familiar with the basics of trading and am ready to take the next step forward.
Trade anytime, anywhere
Stay at the forefront of the crypto market with our intuitive, sophisticated app and web platforms.
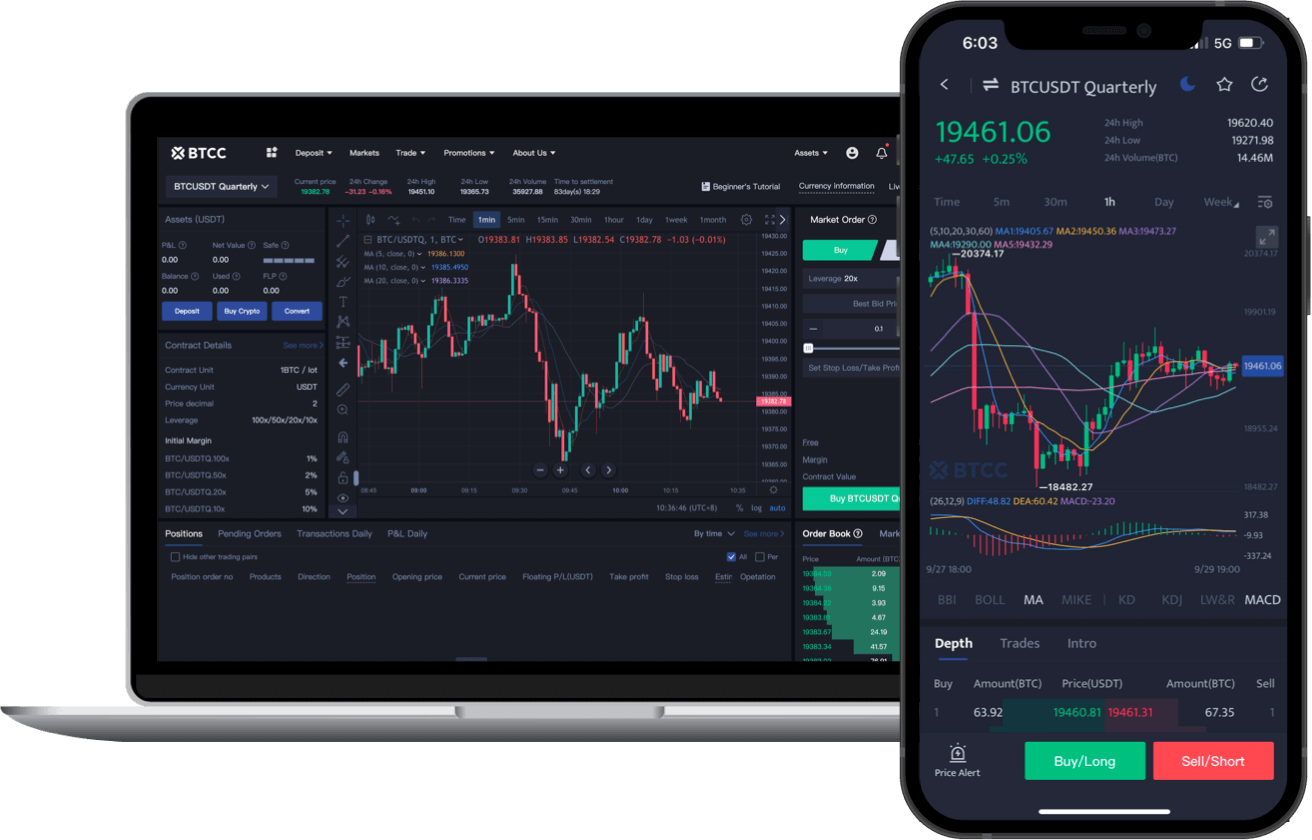
Scan to DownloadiOS & Android
BTCC Updates
We're here to help
Support Centre
See our FAQs for more information about fees, futures trading, and more.
Find out moreOnline Customer Support
Our dedicated specialists are here 24/7 to answer any questions you may have.
Find out moreNew to trading? Get started with low leverage first
- Terms & Agreement
- Customer Service
Quick Links
Risk warning: Digital asset trading is an emerging industry with bright prospects, but it also comes with huge risks as it is a new market. The risk is especially high in leveraged trading since leverage magnifies profits and amplifies risks at the same time. Please make sure you have a thorough understanding of the industry, the leveraged trading models, and the rules of trading before opening a position. Additionally, we strongly recommend that you identify your risk tolerance and only accept the risks you are willing to take. All trading involves risks, so you must be cautious when entering the market.
The world’s longest-running cryptocurrency exchange since 2011 © 2011-2024 BTCC.com. All rights reserved
